As I’ve talked about previously, VMware Horizon is a modern platform for secure delivery of virtual desktops and apps across the hybrid cloud. Horizon provides a range of flexible Data Loss Prevention (DLP) capabilities, to ensure corporate data is secured within your Windows delivered applications.
Some of the DLP capabilities available are:
- Restrict Client Drive redirection
- Restrict Clipboard services to/from the remote client
- Restrict remote USB drives
- Enable/disable printing
- Enable/disable drag and drop to/from the remote client
- Screen Capture Blocking – see here
The purpose of this article is to detail how you can apply these controls for bring your own devices (or BYOD) using the capabilities of VMware Dynamic Environment Manager (DEM)
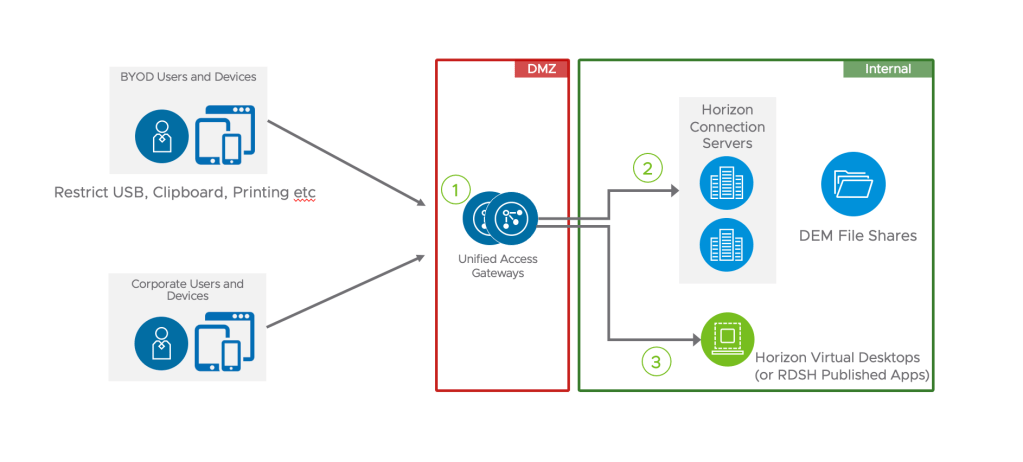
Architecture
A typical architecture is to provide external access for external users to Horizon resources via Unified Access Gateway (UAG) as shown below. What many clients require is to provide more granular control of DLP settings depending on the type of device that is being used externally.
For example, if your staff are using a corporate issued device at home (which typically is managed using a solution such as Workspace ONE or Intune/SCCM) and associated next gen antivirus, then you could allow USB keys, printing and clipboard features.
However, if the user is using their own (un managed) device then you may restrict these features when accessing Horizon remotely (via the UAG).
You may decided that if the user is accessing these resources at the office (on the corporate WiFi) that some items such as printing might be permitted.
Client System Information
When a Horizon Client connects to Windows resources, it send a range of remote client information to the Horizon agent. This is detailed in this kb article. Some of the key information which can be useful are the following Horizon Client Properties:
- Machine_Domain: the remote Windows 10 clients’ domain name
- Machine_Name: the remote Windows 10 client’s PC name
- Broker_GatewayLocation or Client Location which has the value of Internal or External
When you login to a Windows session, you can browse the registry and view this information as follows:
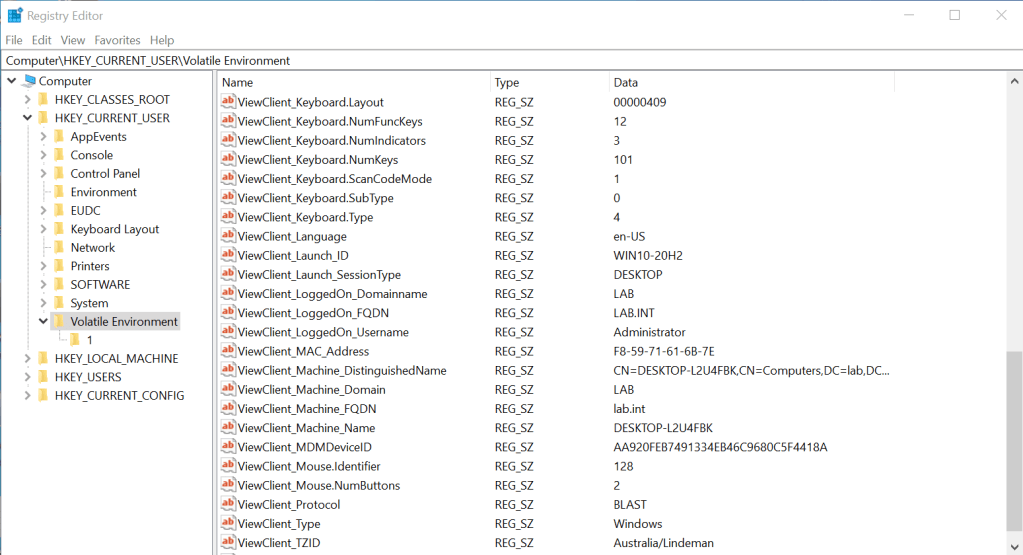
You can see from the above session details, that my remote Windows 10 client is a member of a domain called LAB (lab.int) and the machine name is DESKTOP-L2U4FBK.
So you can use this information to perform some logic such as the following:
- If the remote device is External and is NOT a member of the domain LAB, then we consider this device as a BYOD device. So we could therefore apply DLP restrictions.
- Similarly, if the remote device is External and is NOT has a computer name that doesn’t start with DESKTOP (depending on your corporate standards), then we also consider this device as a BYOD device. So again we can apply DLP restrictions.
Dynamic Environment Manager (DEM) Configuration
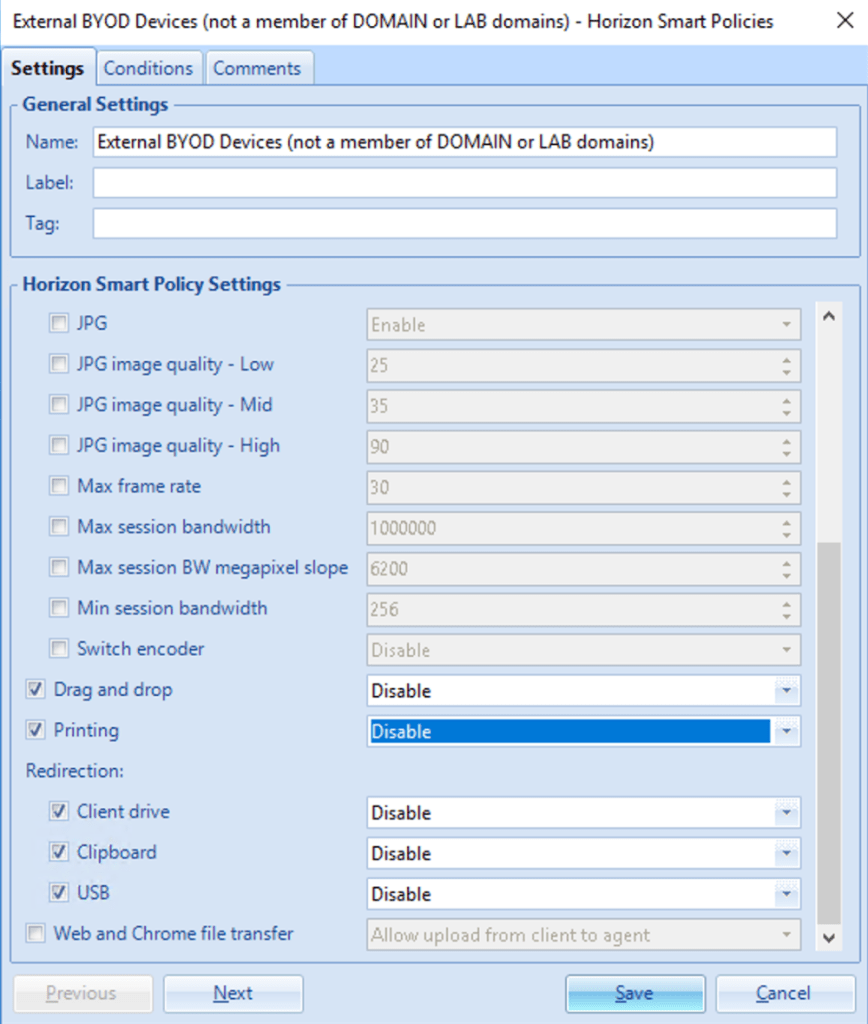
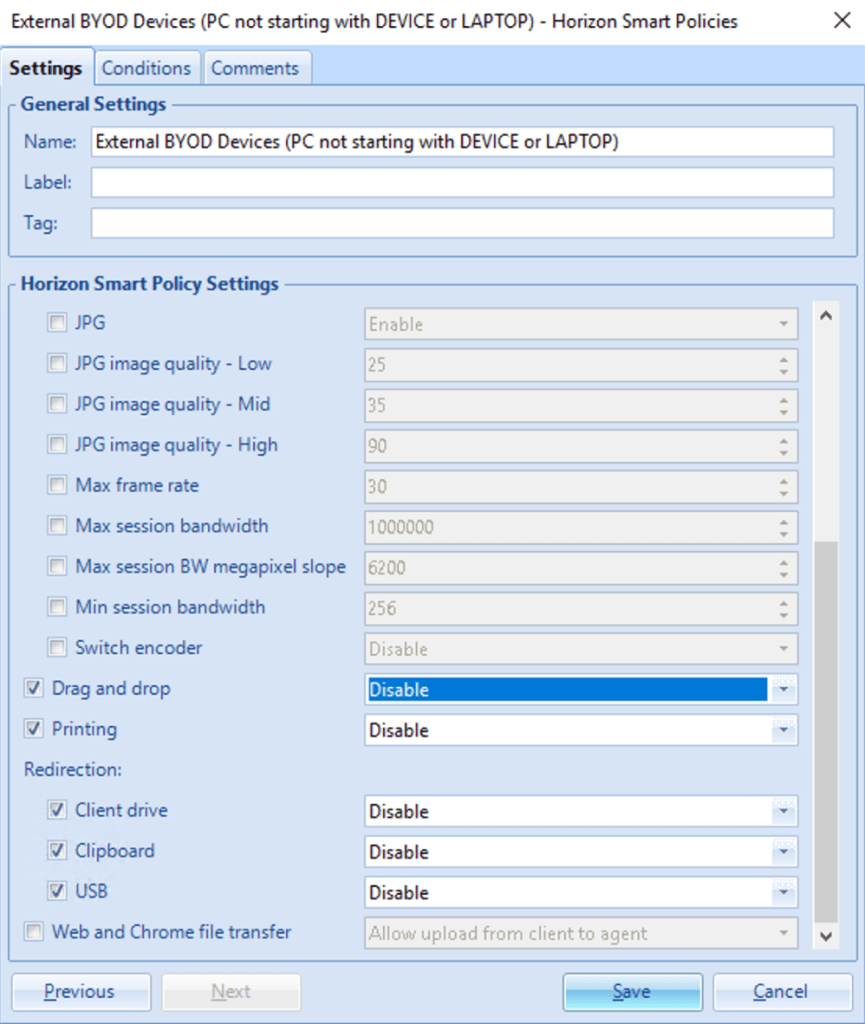
The way this can be achieved using DEM is via Horizon Smart Policies. These policies can leverage the Horizon Client Properties to determine whether a remote device is classified as BYOD, then apply the appropriate restrictions. The following are some screen captures from my lab. I ended up creating two Horizon Smart Polices, using the logic outlined above.
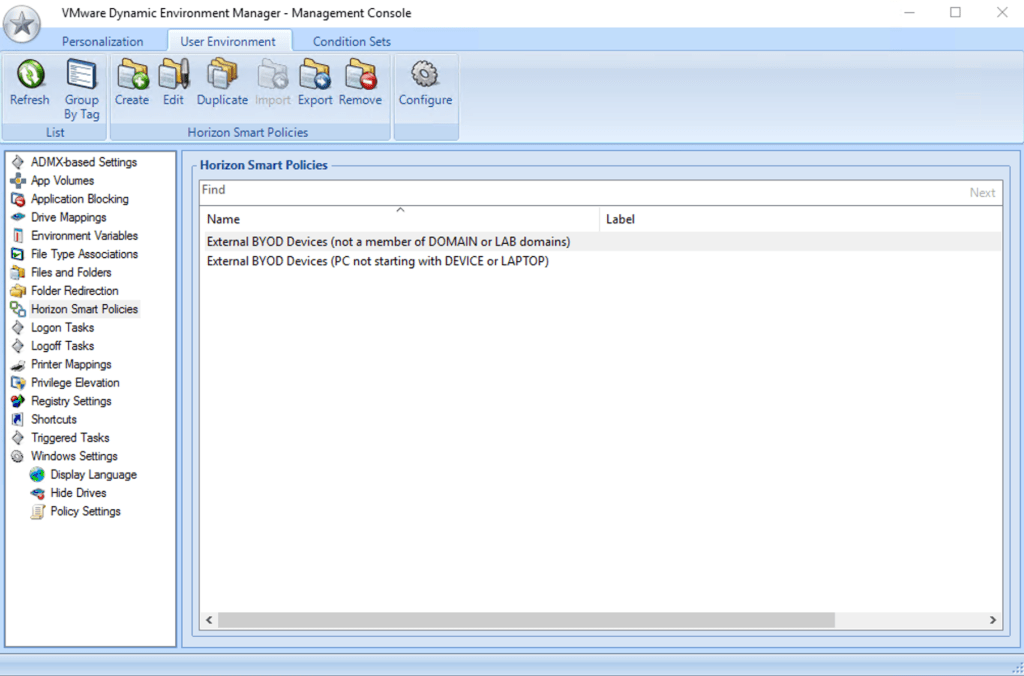
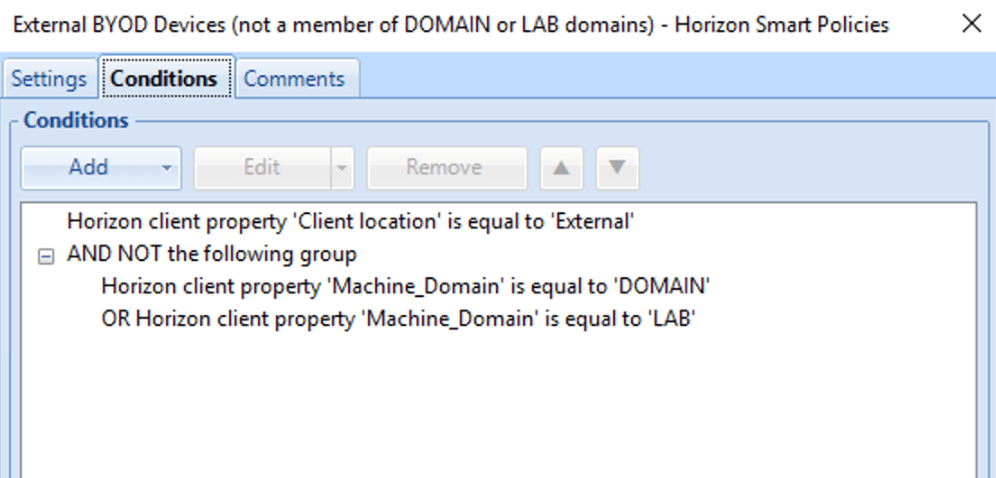
The Horizon Smart Police for determining a BYOD device based on the remote client’s Windows domain membership, and external access was defined as follows:
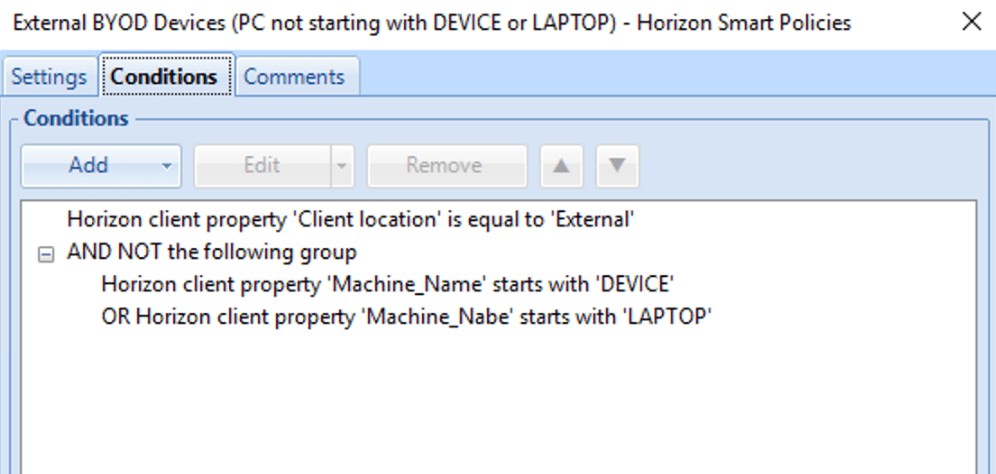
The Horizon Smart Police for determining a BYOD device based on it’s Windows PC name and external access, was defined as follows:
You can review the DEM log files (in DEBUG level) to see how DEM is processing the Horizon Smart Groups. See an extract from lab:
2021-11-11 12:19:40.126 [DEBUG] Conditions: Check for Horizon client property 'Broker_GatewayLocation' = true ('External' is equal to 'External')
2021-11-11 12:19:40.126 [DEBUG] Conditions: Check for Horizon client property 'Machine_Domain' = false ('WORKGROUP' is not equal to 'DOMAIN')
2021-11-11 12:19:40.126 [DEBUG] Conditions: Check for Horizon client property 'Machine_Domain' = false ('WORKGROUP' is not equal to 'LAB')
2021-11-11 12:19:40.126 [DEBUG] Collected Horizon Smart Policies settings for client drive redirection ('External BYOD Devices (not a member of DOMAIN or LAB domains).xml')
2021-11-11 12:19:40.126 [DEBUG] Collected Horizon Smart Policies settings for clipboard ('External BYOD Devices (not a member of DOMAIN or LAB domains).xml')
2021-11-11 12:19:40.126 [DEBUG] Collected Horizon Smart Policies settings for USB redirection ('External BYOD Devices (not a member of DOMAIN or LAB domains).xml')
2021-11-11 12:19:40.128 [DEBUG] Conditions: Check for Horizon client property 'Broker_GatewayLocation' = true ('External' is equal to 'External')
2021-11-11 12:19:40.129 [DEBUG] Conditions: Check for Horizon client property 'Machine_Name' = false ('R8-EHD26' does not start with 'DEVICE')
2021-11-11 12:19:40.129 [DEBUG] Conditions: Check for Horizon client property 'Machine_Nabe' = false (property not available)
2021-11-11 12:19:40.129 [DEBUG] Collected Horizon Smart Policies settings for drag and drop ('External BYOD Devices (PC not starting with DEVICE or LAPTOP).xml')
2021-11-11 12:19:40.129 [DEBUG] Collected Horizon Smart Policies settings for printing ('External BYOD Devices (PC not starting with DEVICE or LAPTOP).xml')
2021-11-11 12:19:40.129 [DEBUG] Collected Horizon Smart Policies settings for client drive redirection ('External BYOD Devices (PC not starting with DEVICE or LAPTOP).xml')
2021-11-11 12:19:40.129 [DEBUG] Collected Horizon Smart Policies settings for clipboard ('External BYOD Devices (PC not starting with DEVICE or LAPTOP).xml')
2021-11-11 12:19:40.129 [DEBUG] Collected Horizon Smart Policies settings for USB redirection ('External BYOD Devices (PC not starting with DEVICE or LAPTOP).xml')
2021-11-11 12:19:40.134 [INFO ] Applied Horizon Smart Policies settings:
2021-11-11 12:19:40.134 [INFO ] Drag and drop is disabled
2021-11-11 12:19:40.134 [INFO ] Printing is disabled
2021-11-11 12:19:40.134 [INFO ] Client drive redirection is disabled
2021-11-11 12:19:40.134 [INFO ] Clipboard redirection is disabled
2021-11-11 12:19:40.134 [INFO ] USB redirection is disabled
Note the remote computer is not a member of the domain called DOMAIN or LAB, likewise machine name is also not starting with DEVICE or LAPTOP, so the smart policies are applied.
Device Posture and OPSWAT
You can also augment the above capability by integrating the UAG with OPSWAT security data. For more information, see the following information – https://www.opswat.com/partners/vmware and kb article to configure this.
Conclusion
Horizon and Dynamic Environment Manager (DEM) provide a great combination of capabilities to apply DLP controls depending on a range of endpoint parameters and location information. I hope this article helps explains how easy it is to setup in your environment.
