The VMware Horizon Cloud Service delivers feature-rich virtual desktops and applications using a purpose-built cloud platform that is scalable across multiple deployment options, including fully managed infrastructure from VMware and public cloud infrastructure from Microsoft Azure.
The following article highlights a number of existing resources and tips and tricks, so you can quickly trial the solution quickly and easily with your existing infrastructure.
Architecture
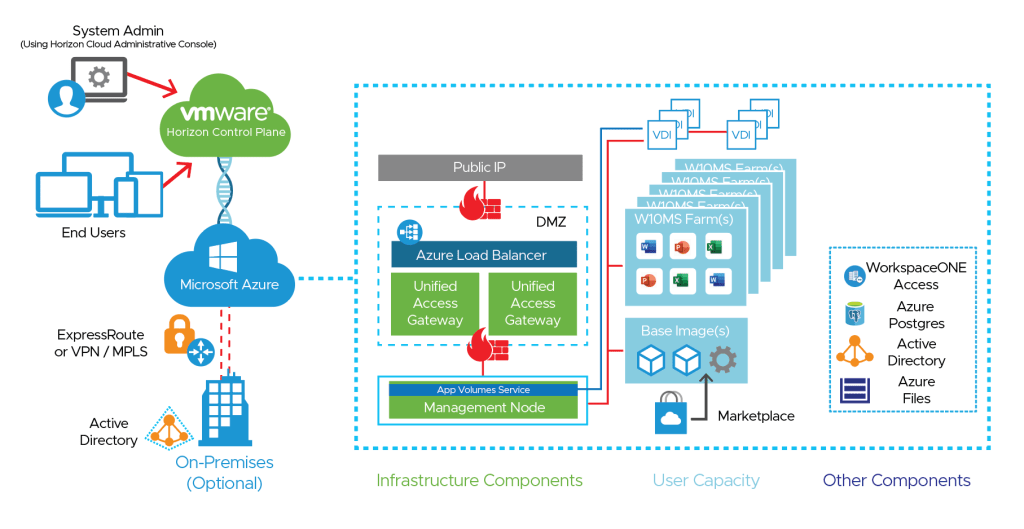
It’s important to understand the architecture of Horizon Cloud on Azure. It consists of a SaaS Horizon Control plane which you can think of as the web administration console. The Horizon service then interacts with a the customers Azure subscription, plus a number of virtual machines running on Azure (in the customers subscription).
For more information on the Horizon Cloud on Azure architecture, see the reference architecture on Techzone.
To trial the Horizon Cloud on Azure service you could run this completely on Azure with a test Active Directory (which some customers like to do) or connect the Azure subscription to your existing on-premises resources and Active Directory using an Azure ExpressRoute or VPN.
Therefore it’s critical to have this Azure networking up and running first before considering a Horizon Cloud on Azure trial.
Horizon Cloud on Azure Prerequisites
The following are the initial prerequisites you’ll need to get your trial activated:
- Azure Subscription (make this a new subscription if you already have other Azure services)
- My VMware account
Provide these details to your VMware End User Computing sales and/or technical team. They will then active your Horizon Cloud on Azure trial. You’ll receive a welcome email with login details (which will be emailed to your My VMware account).
The following are also required for the Horizon Cloud on Azure trial:
- Active Directory + associated groups and accounts defined (see detailed)
- Microsoft Azure VPN/Express Route configured
- In Azure, 3 non-overlapping address ranges in CIDR format in the pod’s VNet, reserved for subnets.
- Management subnet — /27 minimum
- VM subnet – Primary (tenant) — /27 minimum with /24 – /22 preferred, based on the number of desktops and RDS servers
- DMZ subnet — /28 minimum when Unified Access Gateway is deployed in the pod’s VNet (optional)
- NTP server IP address(es)
- DNS server IP address(es)
- FQDN for external user access – ie. horizon.companyname.com
- Certificate or certificates for Unified Access Gateway in PEM format matching the DNS FQDN
The more detailed checklist which you need to thoroughly review is detailed in the VMware Horizon Cloud Service on Microsoft Azure Requirements Checklist For New Pod Deployments. At the time of writing, this guide was for March 2021, so check for any updated guides as required.
It’s very important to have all of your networking and any firewall rules configured before you start. At the time of writing the latest firewall rules are detailed here.
Setting up your trial
Activating Horizon Cloud on Azure consists of completing a step by step wizard. This wizard guides you through activating the service and connecting to your on-premises Active Directory.
However, I’d highly recommend you watch this excellent video put together by Shane Fowler (VMware) titled From Zero to Hero: A Step by Step Guide How To Deploy Horizon Cloud Service on Azure. Shane provides a detailed step by step approach to setting up your trial, including completing a number of pre-requisites on Azure.
If you would like instruction you can follow to setup your own trial, see the Quick-Start Tutorial for VMware Horizon Cloud Service on Microsoft Azure.
Workspace ONE Access
I’d also suggest you enable Workspace ONE Access as part of your Horizon Cloud on Azure trial. This provides the user an easy to use portal where they can get access to Horizon and other Web based applications (with single signon). Below is an example user portal:

To setup Access, I’d recommend following the Workspace ONE Intelligent Hub integration with Universal Broker enabled Horizon Cloud environment by Shrestha Upendra, Sr. EUC Architect, VMware.
This guide details how you activate the Universal Broker, enabling your Access tenant and the user attribute mapping that is required in Access. With this new integration, Horizon virtual application collections are no longer synchronised from the on-premises connector to Access. With the new integration, Horizon entitlements are dynamically displayed for the user when they login to Horizon.
It’s critical however that the user attributes are mapped exactly as shown:
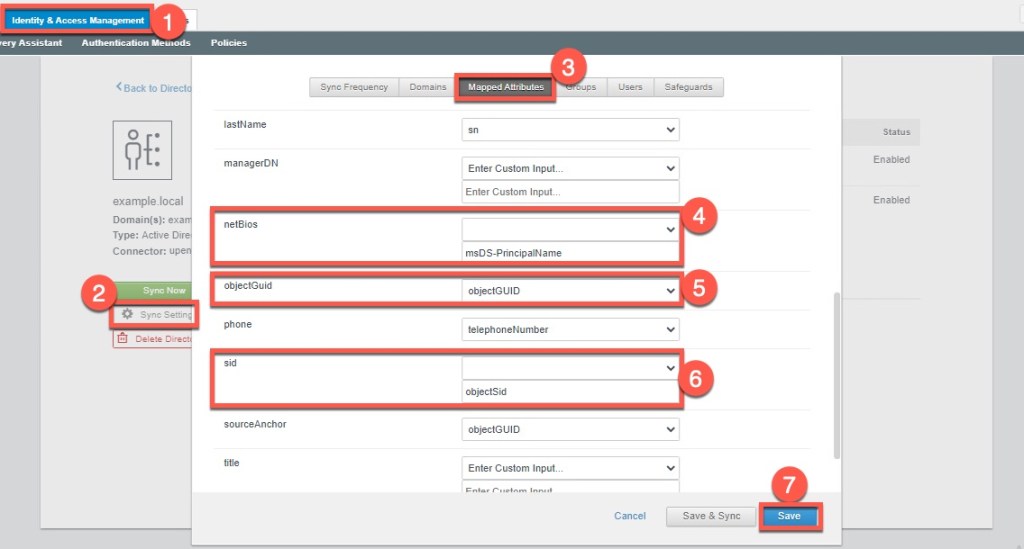
See the Workspace ONE Access – Configure User Attributes for Integration with Horizon Cloud article for further details on the specific mapping.
What if you wanted to have Azure AD as your primary identity provider? Well you can then integrate Workspace ONE Access with Azure AD as a 3rd party IDP. The following article Using Azure AD as a SAML IdP in Workspace ONE Access by Steve D’Sa provides you step by step instructions on how to set this up.
Azure AD can request MFA for a user (using Microsoft Authenticator) if required.
Dynamic Environment Manager (DEM)
Dynamic Environment Manager (DEM) is worthwhile testing as part of your trail. DEM essentially delivers a personalized experience to a non-persistent desktop. DEM simply requires a file server with two file shares. The DEM quickstart guide provides you with the detailed instructions to configure and setup DEM.
App Volumes
The following is a link to the VMware documentation. However, I’d recommend that you check out another great article by Shrestha Upendra titled Application Life Cycle Management in VMware Horizon Cloud on Azure.
Getting Started with the Console
The following article titled VMware Horizon Cloud on Microsoft Azure Cheat Sheet for Horizon 8 Administrators is a great way to become familiar with the console, particularly if you’re experienced with using Horizon 8 (on-premises).
Conclusion
After completing these sections (and leveraging a range of excellent blogs and VMware resources) you should have successfully setup your Horizon Cloud on Azure tenant.
If you have any further queries on Horizon, I’d recommend posting them on the Horizon Communities forum. Feel free to contact me if you have any feedback or corrections too.
Updates
Since writing this blog article, VMware has published the following Evaluation Guide for VMware Horizon Cloud Service on Microsoft Azure with a series of step by step videos. Check it out!
