Many organisations need to deploy iPhone or iPad devices to their field workers, so they can perform their job whilst on the move. Apple devices allow them to access corporate information quickly and easily, using the easy to use iOS operating system.
iPad devices can also be configured as kiosk terminals, so only selected mobile apps or web pages are displayed on the device.

The purposes of this article is to step you through the entire configuration process using Workspace ONE UEM, so you can deploy large number of devices quickly and easily. Then provide your company the platform to manage them remotely.
I’d like to thank Dany Leclerc, Pratheep Vinayagamoorthy and Eri Ang for helping confirm various configuration settings mentioned in this article (which weren’t documented in a single place previously).
Apple Push Notification Service (APNs)
As detailed in the Getting Started with Workspace ONE UEM guide, Apple Push Notification service (APNs) is the messaging protocol created by Apple to manage mobile devices. To manage iOS devices, Workspace ONE UEM requires a valid APNs certificate. This exercise helps you to generate the APNs certificate.
- In Workspace ONE UEM Console, navigate to Getting Started > Workspace ONE. Navigate to Apple Push Notification Service (APNs) and click Configure
- Navigate to Apple Push Notification Service (APNs) and click Configure.
- Under Download Certificate Request, click MDM_APNsRequest.plist. Click Continue. Save this file to your computer.
- Enter your corporate Apple ID email address that you will use to manage all Apple devices for your organization. If you do not have a corporate Apple ID, Create an Account with Apple.
Important: Do not use a personal Apple ID. If the user leaves the organization and you cannot renew the certificate, you must re-enroll all iOS devices!
- Go to the Apple Push Certificates Portal and use your corporate Apple ID credentials to authenticate. Complete the following steps to create the APNs certificate.
- Enter your corporate Apple ID
- Enter your Apple ID password
- Click Sign In.
- Click Create a Certificate.
- Click Choose File and select the MDM_APNsRequest.plist you downloaded previously.
- Click Upload.
- The Apple Push Certificates Portal will issue you with a certificate. Click Download.
- Return to the Getting Started wizard in the Workspace ONE UEM console, and click Next.
- Click Upload.
- Click Choose File and select the previously downloaded .pem file.
- Click Save.
- Enter your Apple ID. For example, appleid@vmware.com.
- Click Save.
- Enter the security PIN, if prompted.
- You should be redirected to Devices & Users > Apple > APNs for MDM. If not, navigate to that location and click Test Connection.
You can now manually enrolled an iOS or iPadOS device into Workspace ONE UEM.
Automated Device Enrollment Setup
Automated Device Enrolment from Apple (previously known as Device Enrolment Program or DEP) lets you automate enrolment into Workspace ONE UEM and simplify initial device setup. You can supervise devices during activation without touching them, and lock MDM enrolment for ongoing management.
You’ll need to have an Apple Business Manager account. The following article from Apple details how to obtain one.
The following video titled Workspace ONE UEM: Auto-Device Enrollment – Feature Walk-through shows you how to set this up with Workspace ONE UEM.
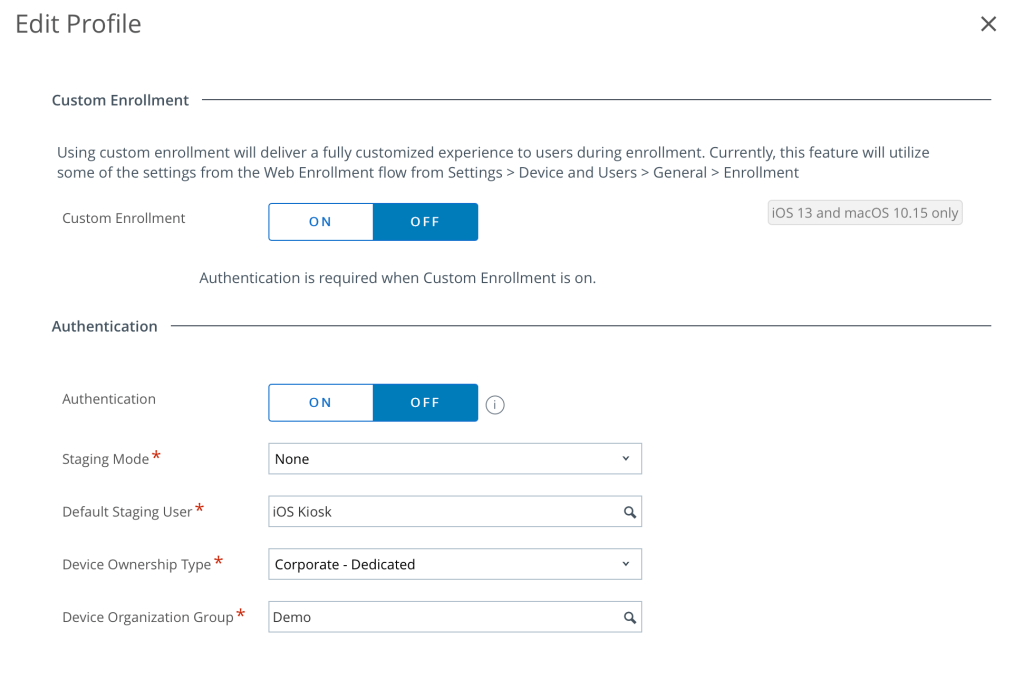
For the purposes of setting up a device as a kiosk (no authentication) I configured the following for my DEP profile settings:
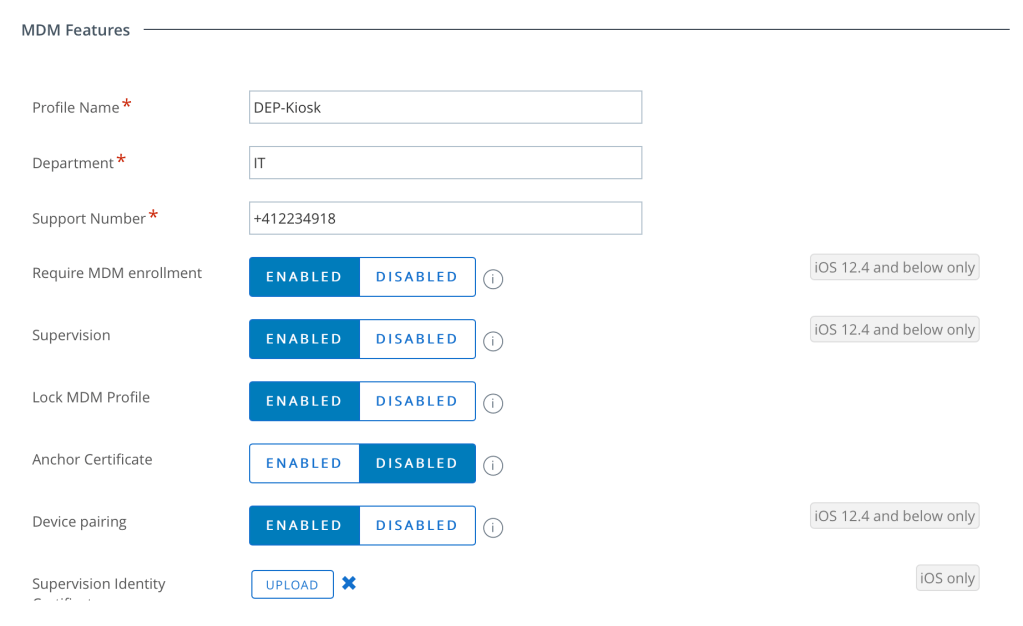
You’ll also want to ensure you enable Supervision of the devices and likely Enable the Lock MDM Profile setting too:
Note that I set a default staging user called iOS Kiosk which was a basic user in Workspace ONE UEM as follows:

If you have added you iOS devices to Apple Business Manager (ABM) and those devices have synchronised through to Workspace ONE UEM, you should then be able to turn on a new device and it will enrol automatically.
What if I don’t have a device added to ABM? (for example, I have an existing iOS device). Then see this very useful video titled VMware Workspace ONE UEM 9.2: DEP Registration in iOS 11 – Feature Walk-through on how to do this.
Setup Volume Purchase Program (VPP) Managed Distribution
We’ll now integrate Apple VPP within Workspace ONE so that we can distribute public iOS applications (including the Workspace UEM UEM Hub) without the user needing to login with their Apple ID to receive any applications.
In Workspace ONE UEM:
- Click Groups & Settings.
- Click Configurations.
- Scroll down through the list of Configurations.
- Select VPP Managed Distribution
- Ensure the Current Setting is set to Override.
- Enter a friendly name for the Location.
- Click Upload.
- In the dialog box, click Choose File. Browse to and select the vpptoken file downloaded in Download Token from Apple Business Manager, and select Choose.
- Click Save.
- Click Save.
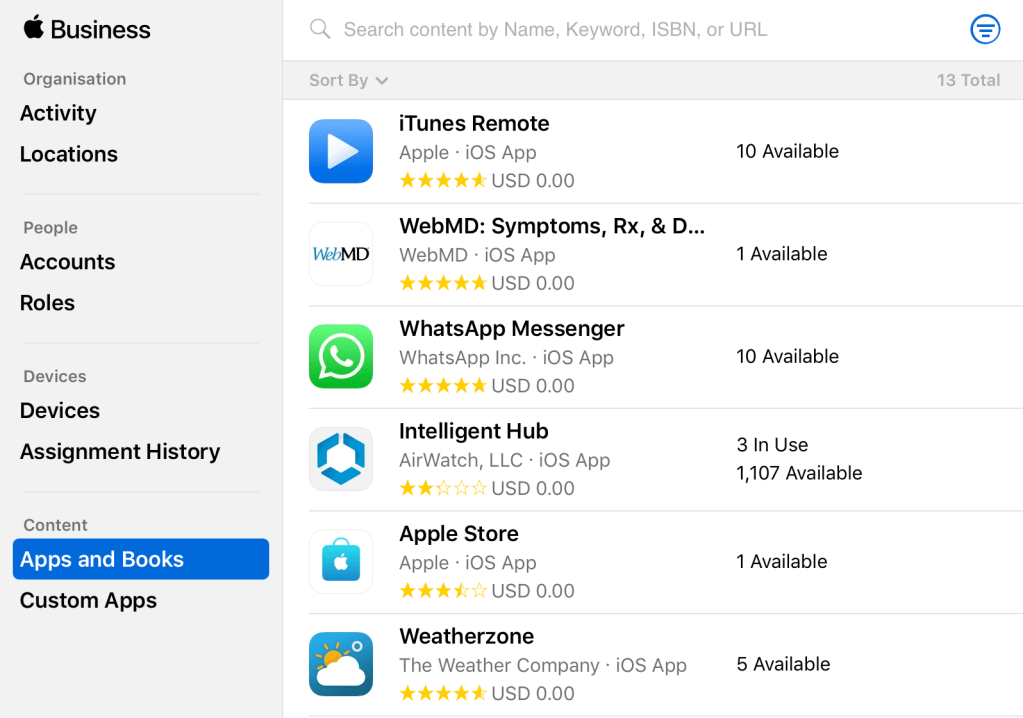
Within ABM, add your public iOS applications such as the Intelligent Hub. Add any other public apps as required:
By default, Workspace ONE syncs managed distribution licenses for custom apps and volume-licensed public apps daily. The sync is scheduled automatically, allowing Workspace ONE to reconcile newly purchased licenses and updated metadata (descriptions and images). When you upload a location token, you can speed up this process by manually initiating a license sync.

Managed distribution licenses can be assigned on a per-user, or per-device basis. For the per-user licensing model, the end-user of the device is prompted to enter their Apple ID credentials into the device to assign the license. In other words, per-user license distribution requires that all users have an Apple ID.
What we want however is the per-device licensing model. In this case the managed distribution licenses are assigned directly to the device regardless of whether the user has entered Apple ID information. The end-user is not required to have an Apple ID in order for the app to be assigned to the device and installed from the App Store.
Select a number of applications and select Enable Device Assignment
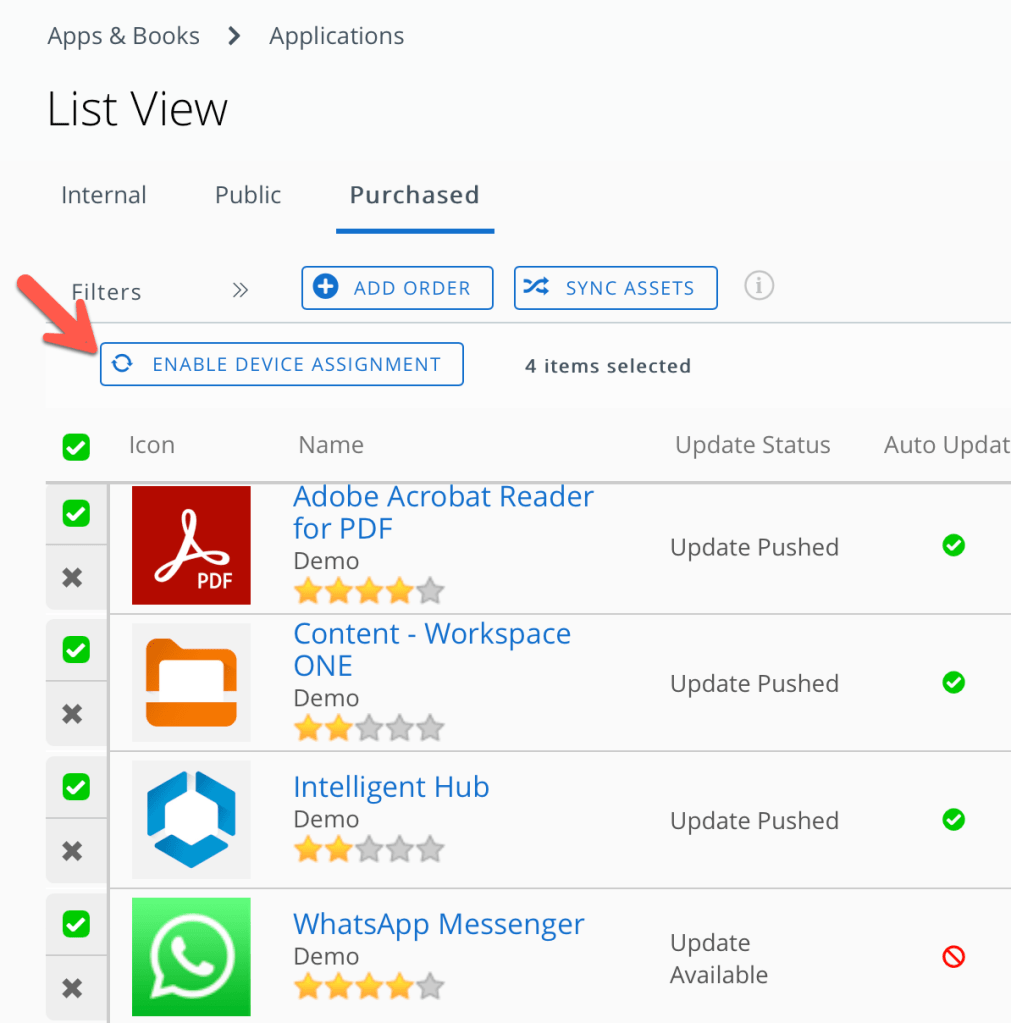
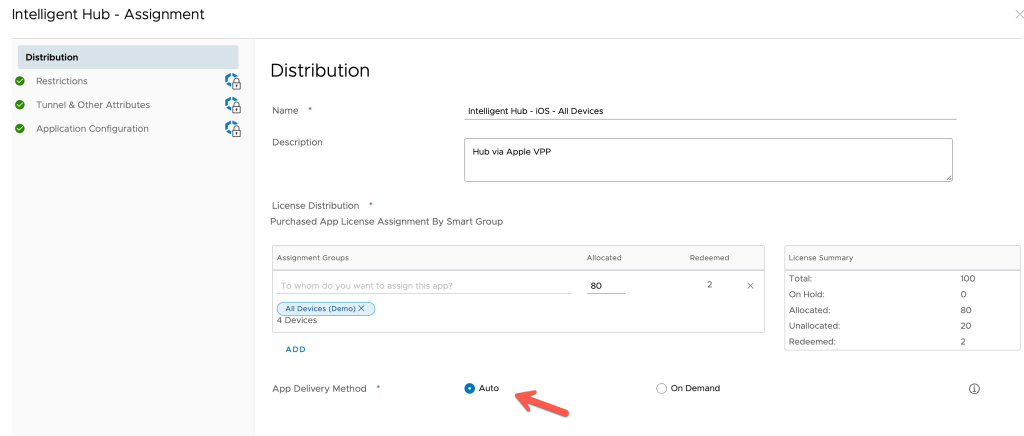
For your applications you’ll want to assign them to All Devices and set the distribution to Auto, so the applications are deployed when the device is enrolled into Workspace ONE UEM.
I’d recommend you perform a full wipe of the device, then test the device automatically enrols into Workspace ONE UEM and the Hub is automatically deployed.
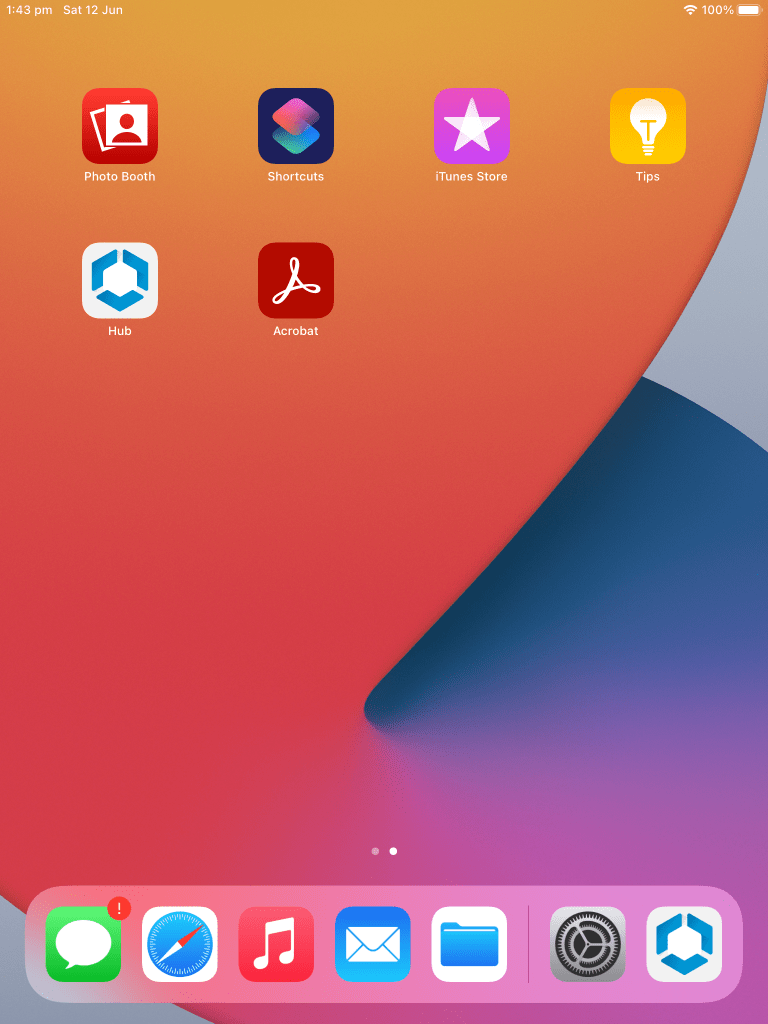
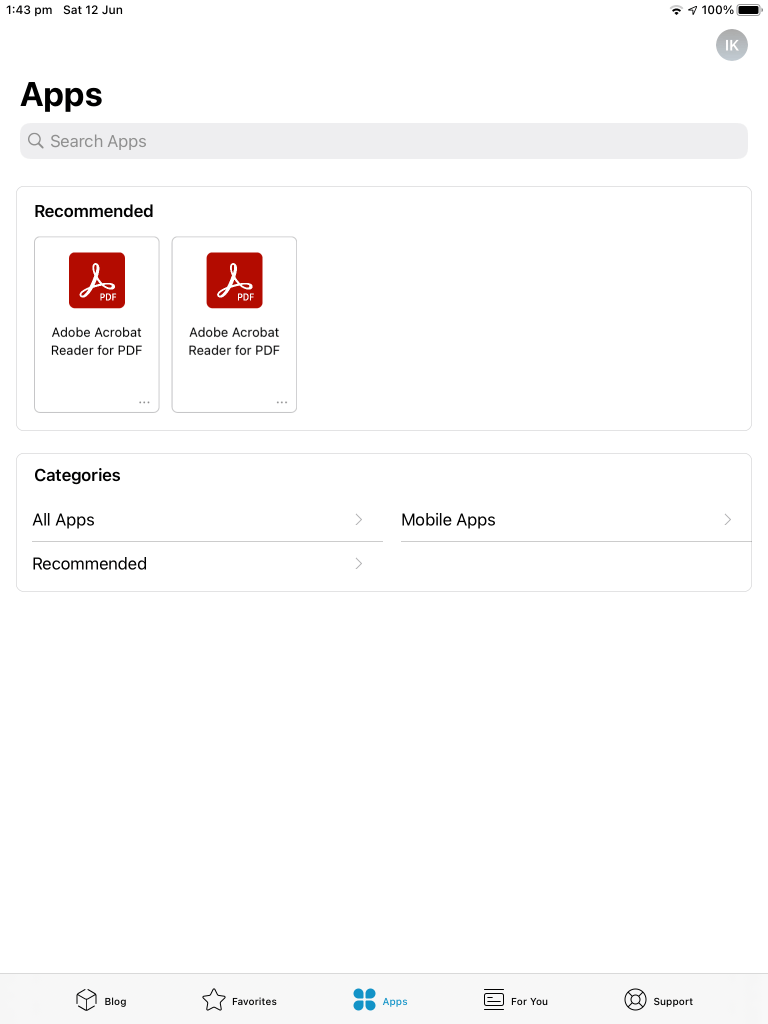
The following are two images from my test iPad:
Remote Support with Workspace ONE Assist
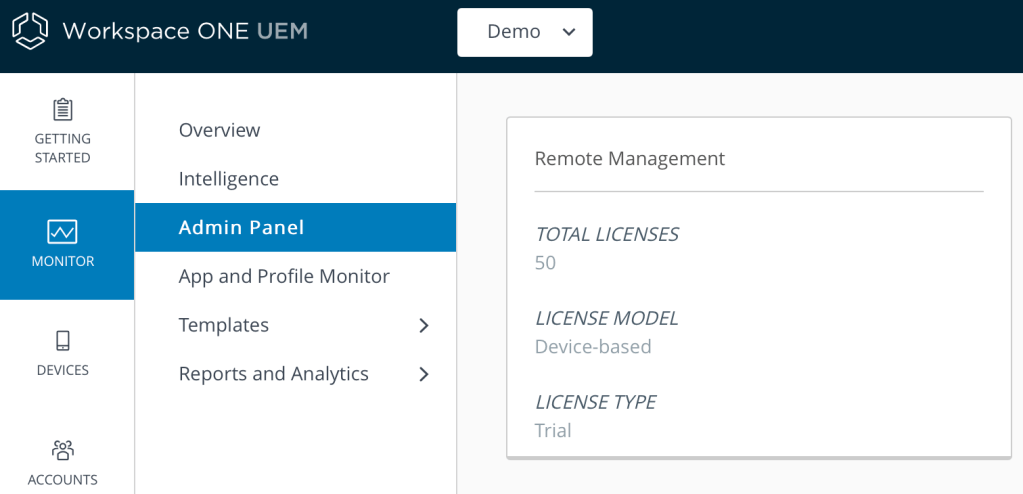
If you’ve purchased Workspace ONE Assist, you’ll see the licenses activated in the Admin Panel as shown:
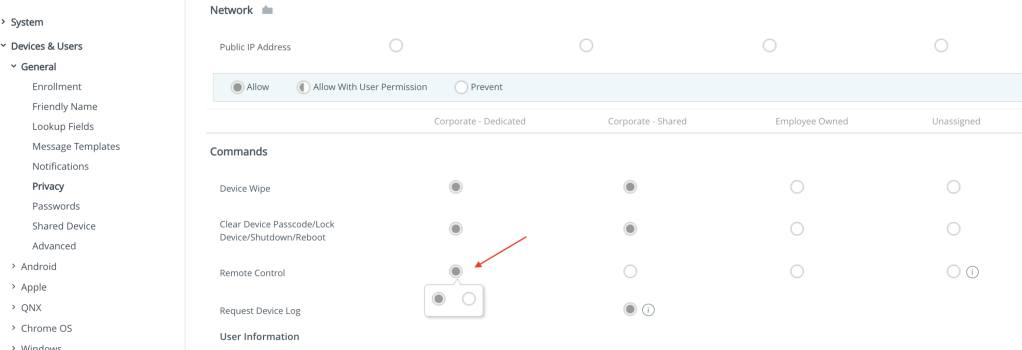
(If applicable) Under Groups and Settings > Devices & Users > General > Privacy, ensure you have the Privacy setting enabled (dark circle) against Remote Control as shown below.
Now from the UEM console, find your device from the Devices menu. Select your device then select Remote Assist as shown:

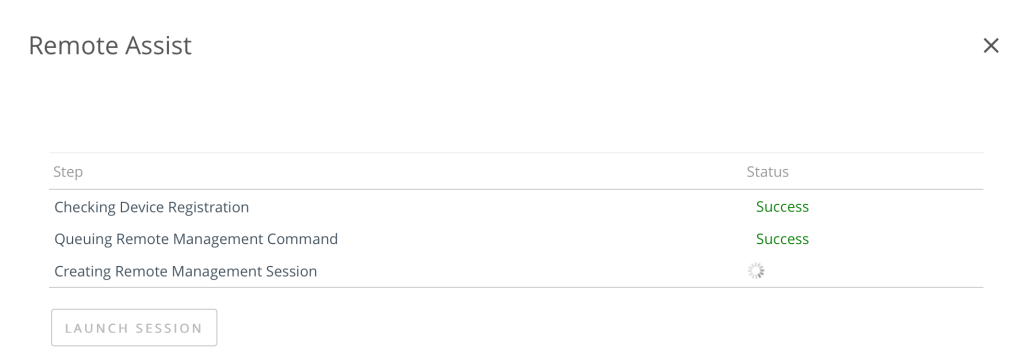
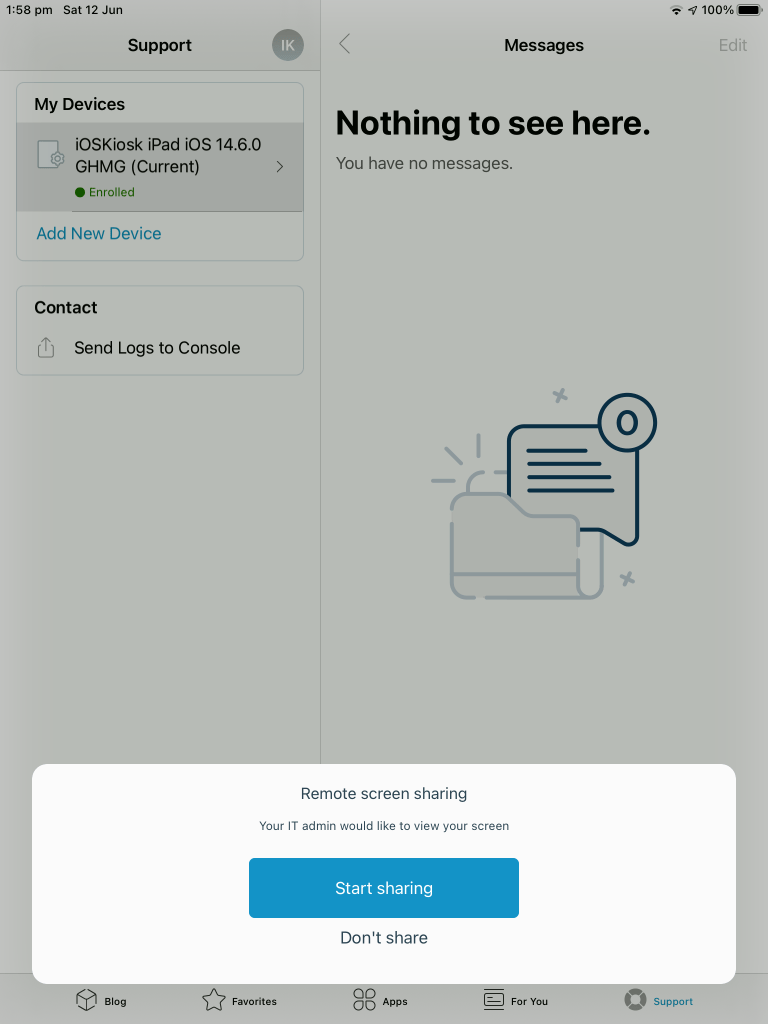
Ensure your web browser is not blocking any pop up screens. You should then see it attempt to connect to the device as shown:
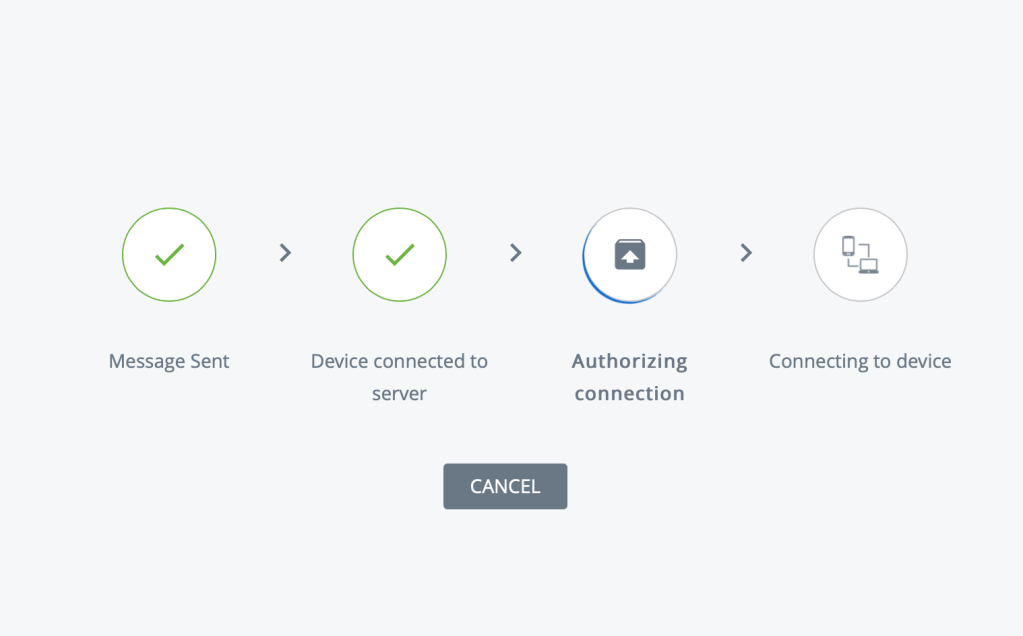
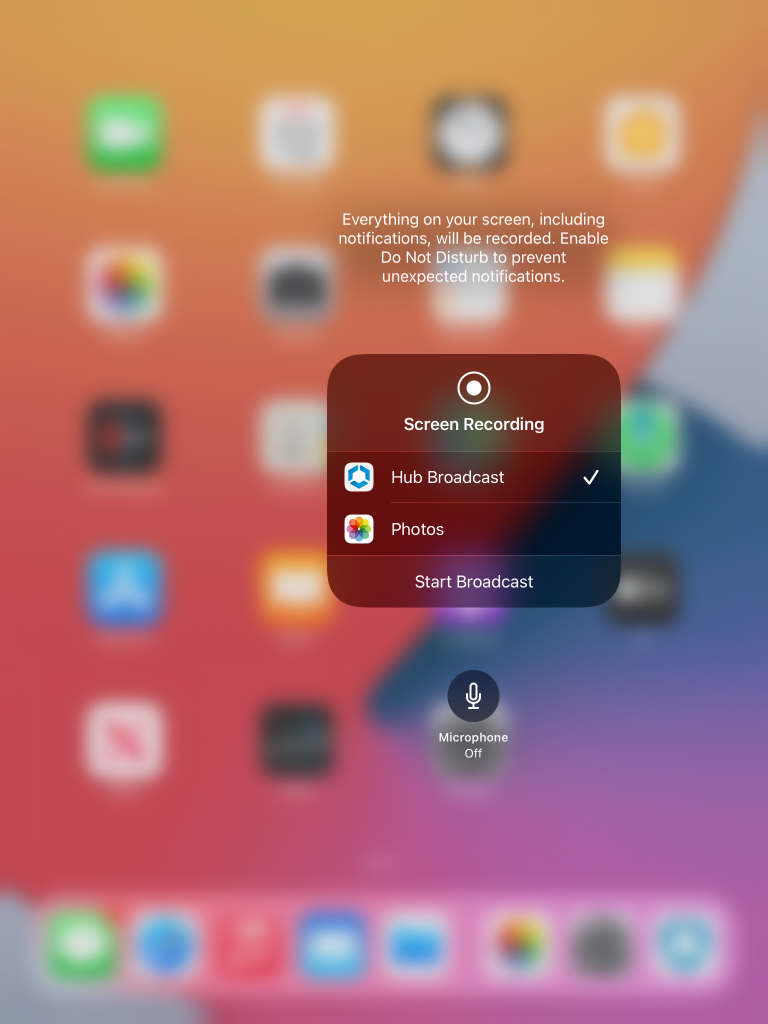
The great news is that Assist is built into the Hub application itself. Previously you needed to enable the Screen Recording option within your iOS device as per this article. However with iOS Hub version 20.11 or later and iOS 13, this is no longer required… yay!
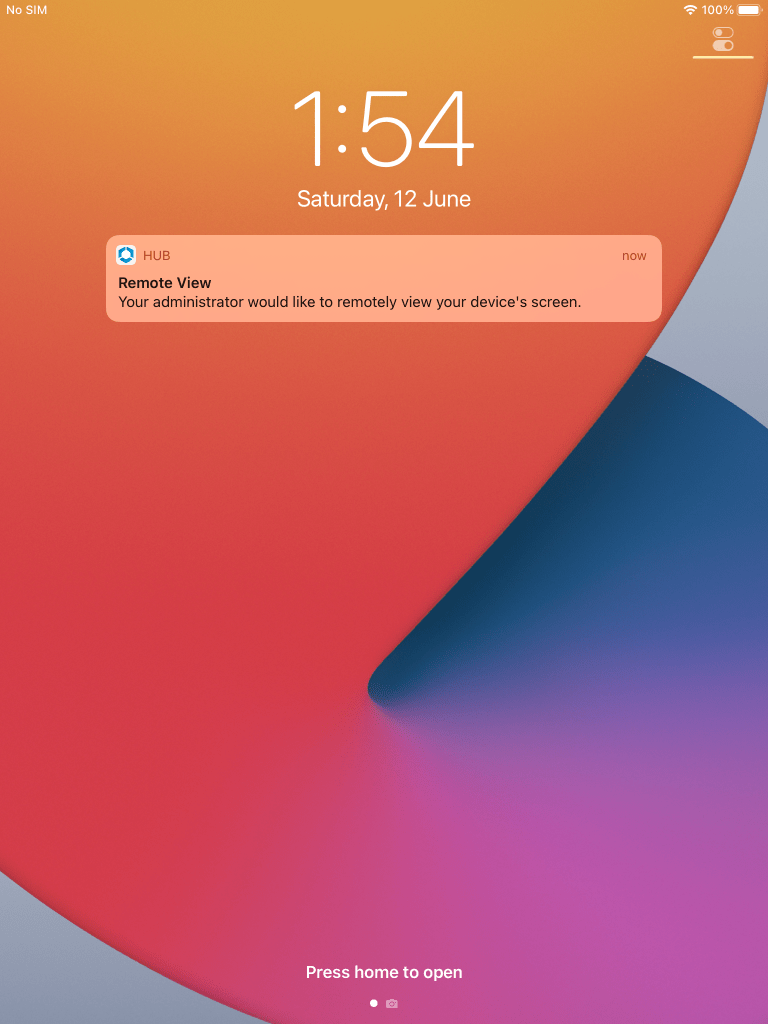
On the iPad, you should hear a sound and see messages as per the following. Select Start Sharing then on the Screen Recording option with Hub Broadcast selected, tap on Start Broadcast to initiate the remote view of the iPad’s screen:
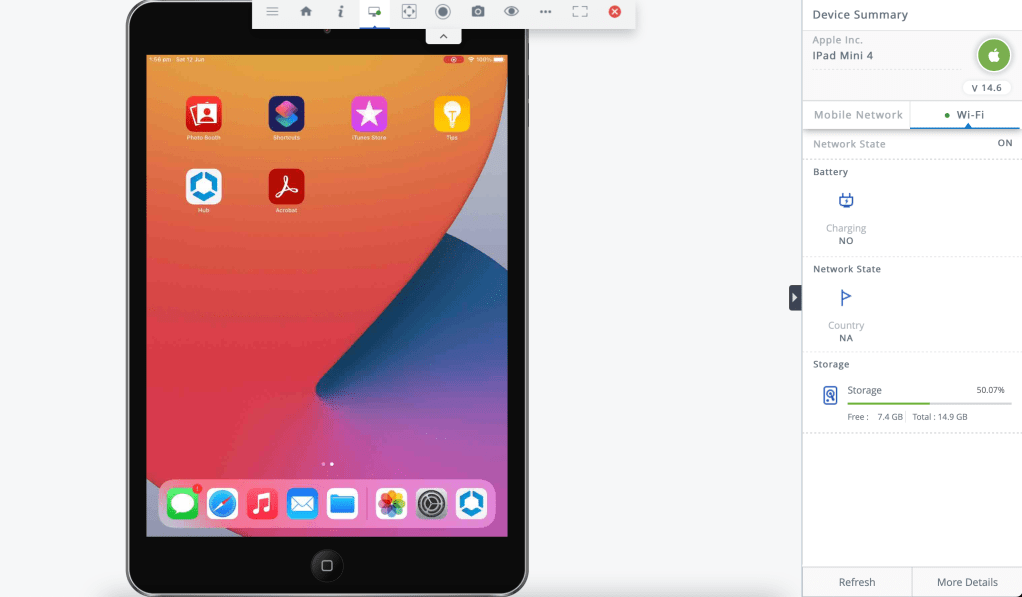
Then from the Workspace ONE UEM console you’ll be able to remotely view the iPad’s screen as shown:
What if I get any errors when trying to initiate an Assist session? Ensure the Hub is first started on the iOS device. This can take a short time to then register the device with the Assist server. Try again and it should then work.
Device Policies
It is recommended to set some device policies such as minimum passcode and other applicable settings for your devices such as WiFi, VPN etc.

Single Application Kiosk Mode or Showing Selected Apps
Workspace ONE UEM can configure your iOS or iPadOS devices to present a single application as the primary interaction for users. The user will only have access to the application, and cannot access the device’s Springboard. This configuration is used to create a kiosk or digital signage using your iOS and iPadOS devices.
- Navigate to Devices > Profiles & Resources > Profiles > Add > Add Profile > iOS.
- In the General Tab, provide a name for the profile and assign the profile to smart groups that include your kiosk devices.
- Select the Single App Mode payload, and select Configure.
- Select Lock device into a single app.
- Type the Bundle ID of the application that the devices need to be locked to.Note: By default, all functions on the device will be configured to be disabled. You may choose to enable any particular setting if necessary for your custom needs. Else, proceed to Save and Publish.
- Select Save to complete the Launcher configuration.
- Select Save and Publish.
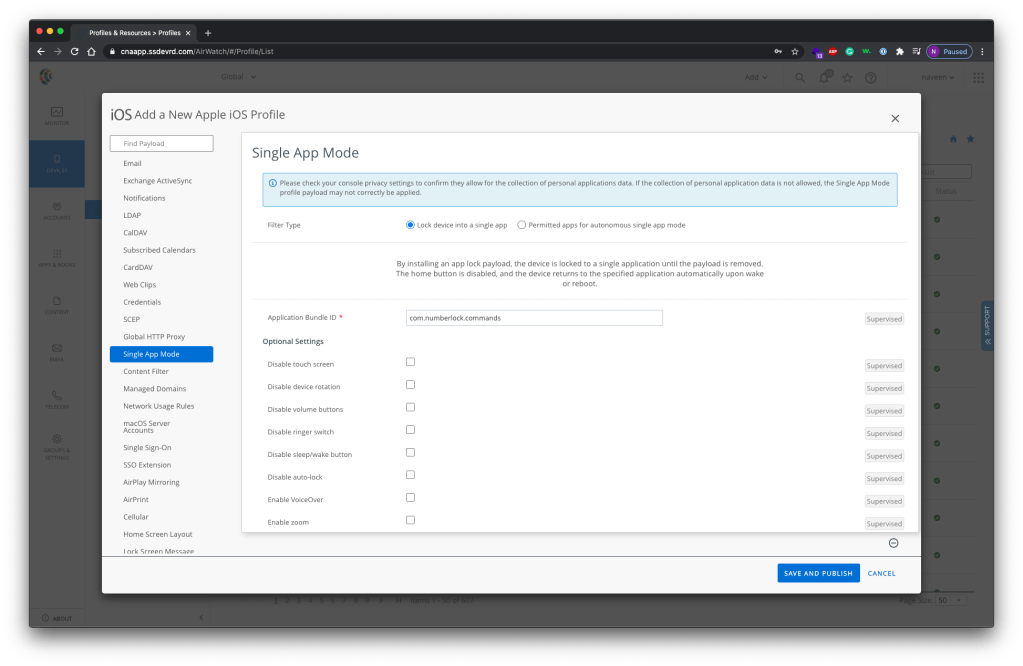
In this mode, Assist will not be operational since it needs to allowed to run on the device.
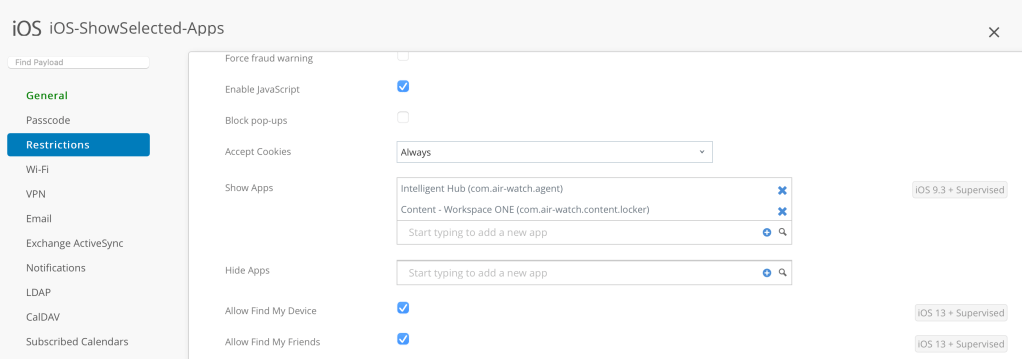
The alternative is to show and hide applications on iOS instead. That way you ensure that only corporate applications are accessible on the device by creating the following profile. I’ve shown what it looks like on the iPad too:

No Authentication?
You will have observed that the iPads haven’t required any form of authentication when the device is setup.
For your company, you might with to enable authentication so that a userid/password must be provided to activate the iOS device during the initial iOS setup phase. This is enabled on the UEM console as follows:
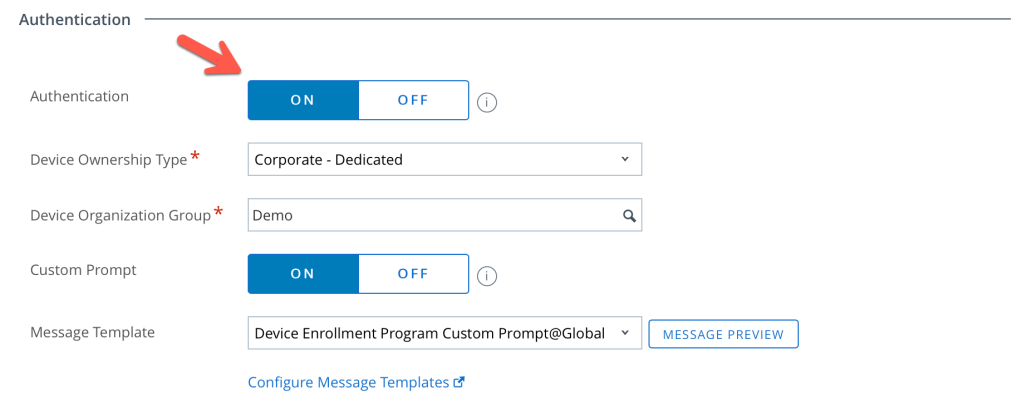
The following photo shows the authentication screen during the iOS DEP enrolment process:

Conclusion
That’s it! You can now easily deploy your iPads to your field workers and remotely support them (as long as they have some form of Internet connection).
Acknowledgement: Main iPad image with rugged case from link
Updates
See the following article on VMware docs titled Configure Shared iOS Devices for your Shift Workers which details the Hub Check-in Check-out feature, plus the native iOS Shared iPads for Business capabilities.
